News: All News
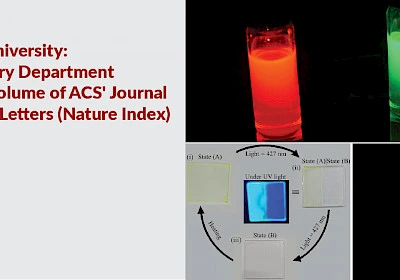
Huge Milestone for University: Six papers by Chemistry Department published in a single volume of ACS' Journal of Physical Chemistry Letters (Nature Index)
The Department of Chemistry at the School of Natural Sciences, Shiv Nadar Institute of Eminence (SNIoE) fosters a dynamic environment for...
Professor Dupré speaks on 'Human Processes' at third edition of Global Futures Lecture Series
Dr. John Dupré, Professor of the Philosophy of Science at the University of Exeter, delivered a lecture on 'Human Processes' at the India Habitat...
Department of Physics Hosted a 4-day international conference on sustainable nanomaterials integration & Organisation for energy & environment
The Department of Physics at the Shiv Nadar Institution of Eminence Deemed to be University (SNIoE), in partnership with UNSW Sydney, Australia,...
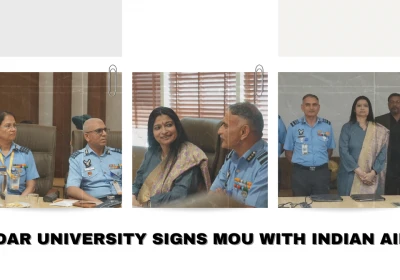
Shiv Nadar University signs MoU with Indian Air Force
Acknowledging the selfless service of Indian Air Force personnel for their contributions, Shiv Nadar Institution of Eminence, the Indian Air Force...
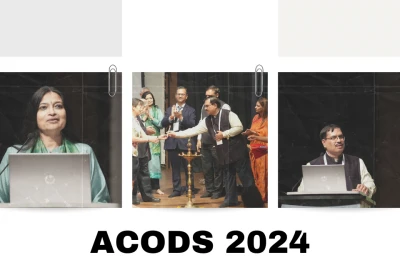
Shiv Nadar University hosts biannual ACODS 2024 conference
The breakneck speed of technological advances notwithstanding, control engineering experts spent four days brainstorming at Shiv Nadar University...
Bahar Dutt wins the prestigious AAAS Kavli Science Journalism Award
Bahar Dutt, Associate Professor at Shiv Nadar University’s School of Humanities and Social Sciences has won the prestigious American Association...
Shiv Nadar University inks MoU with Bharat Petroleum's Corporate Research & Development Centre
In a collaboration to extend industrial and scientific innovation, Shiv Nadar University inked an MoU with the Corporate Research & Development...
Experts discuss new frontiers in cellular and molecular mechanisms of regeneration at 3-day conference
Nearly 60 experts from across the world delivered talks during the 3-day Conference on Cellular and Molecular Mechanisms of Development and...
Dr. Samarendra Pratap Singh Advocates for Solar Cell Technology Advancement
In a recent article published in PV Magazine, Dr. Samarendra Pratap Singh, Professor, Department of Physics at Shiv Nadar University, sheds light...
Shiv Nadar University hosts inaugural event of Gender and STEM initiative
Shiv Nadar University on Saturday held the inaugural event of its Gender and STEM Initiative at India Habitat Center, New Delhi. The event, held a...
Triumph on the Track: Shiv Nadar University Hosts Thrilling External Staff Sports Spectacle!
The Department of Physical Education at Shiv Nadar University proudly organized the External Staff Sports Meet on January 25th and 26th, 2024....
Shiv Nadar University's Industry Partnership Summit explores new avenues
The inaugural Industry Partnership Summit held by Shiv Nadar University at Hyatt Regency on Friday (January 19) on the theme of 'Innovate, Educate,...
Glimpses of the admission info session at Shiv Nadar University
Bitter cold and foggy conditions weren't a dampener as parents and prospective students streamed into the campus on Sunday (January 14) to attend...
Shiv Nadar University hosts school students at 6-day residential Winter School
The winter school provided students from Class 7 to Class 12 with a holistic experience to nurture both academic growth and personal development....
Shiv Nadar University alums get together for annual reunion
“Words fail to explain the feelings I am experiencing. It is like meeting someone with whom you were living for four years,” says Sarthak...
Shiv Nadar University Squash Stars Set to Shine at Khelo India Youth Games 2024 in Tamil Nadu
We are proud to announce that Meyyappan L, Abhay S Vasudev, and Cheazerina Benjamin from Shiv Nadar Institution of Eminence have been selected for...
Shiv Nadar University students make the best of summer opportunities worldwide
When Vasundhara Verma, a fourth-year Life Sciences student of Shiv Nadar University, first stepped onto the University Of Heidelberg campus this...
Department of History and Archaeology & School of Humanities and Social Sciences Offers Fatima Hamid Fieldwork Grant 2023-24: Applications Open
Fatima Hamid joined the Department of History, Shiv Nadar University as a PhD research scholar in August 2021 to work on a project on the history...
University hosts academic leadership of 11 global institutions
The university on Friday (October 13) hosted the academic leadership of 11 global institutions for a discussion on diversity in university...
Dr. Upendra Pandey, Assistant Professor, Department of Electrical Engineering Elected as a member of National Academy of Sciences India (NASI)
Dr. Upendra Kumar Pandey, Assistant Professor, Department of Electrical Engineering, Shiv Nadar Institution of Eminence (Deemed to be University),...
Shiv Nadar University begins talk series ‘From the Diplomat’s Perch’ with German envoy
On Friday (September 22), German Ambassador to India Dr. Philipp Ackermann kicked off Shiv Nadar University’s talk series ‘From the...
Dr. Debdas Ray, Associate Professor, Department of Chemistry Elected as a member of National Academy of Science India (NASI)
Dr. Debdas Ray, Associate Professor, Department of Chemistry, Shiv Nadar Institution of Eminence (Deemed to be University), has been Elected as a...
Professor Parthapratim Munshi, Ph.D. FRSC, Department of Chemistry appointed Co-Editor of the "Journal of Applied Crystallography"
Professor Parthapratim Munshi, Ph.D. FRSC, Department of Chemistry, School of Natural Sciences, Shiv Nadar University, has been appointed...
Dr. Sethi speaks about AI at second edition of Global Futures Lecture Series
Demystifying the apprehensions and explaining the opportunities offered by Artificial Intelligence in the field of design, Dr. Suresh Sethi,...
Placement Brochure 2023-24: Department of Economics
Placement Information 2023-24 Warm greetings from the Placement Cell at the Department of Economics, Shiv Nadar Institution of Eminence! We are...
133 students present papers at 9th Opportunity for Undergraduate Programmes Conference
Spread across September 9 and 10, Shiv Nadar University saw undergraduate students presenting 133 projects as part of the 9th edition of the...
Shiv Nadar University's Inaugural 10K Challenge a grand success
The day began very early at Shiv Nadar University on Sunday (September 3) when over 1,200 participants in the inaugural 10K Challenge...
Shiv Nadar University’s 2023 Faculty Professional Development Program marks the completion of its first year as an Institution of Eminence
Opening the program on July 31, 2023, Vice-Chancellor Dr. Ananya Mukherjee, said, “Faculty is the pillar of any academic institution. It is...
Shiv Nadar Institution of Eminence Celebrates Ninth Convocation
Greater Noida, 31st July 2023: India's youngest Institution of Eminence, Shiv Nadar IoE, marked a significant milestone as it marched into its...
Shiv Nadar University takes the top spot in the private domain under Careers 360 Young Universities Ranking 2023
Shiv Nadar University ranked number one as India’s Best Young University (Private) by Careers 360 Young Universities Ranking 2023. It is also...